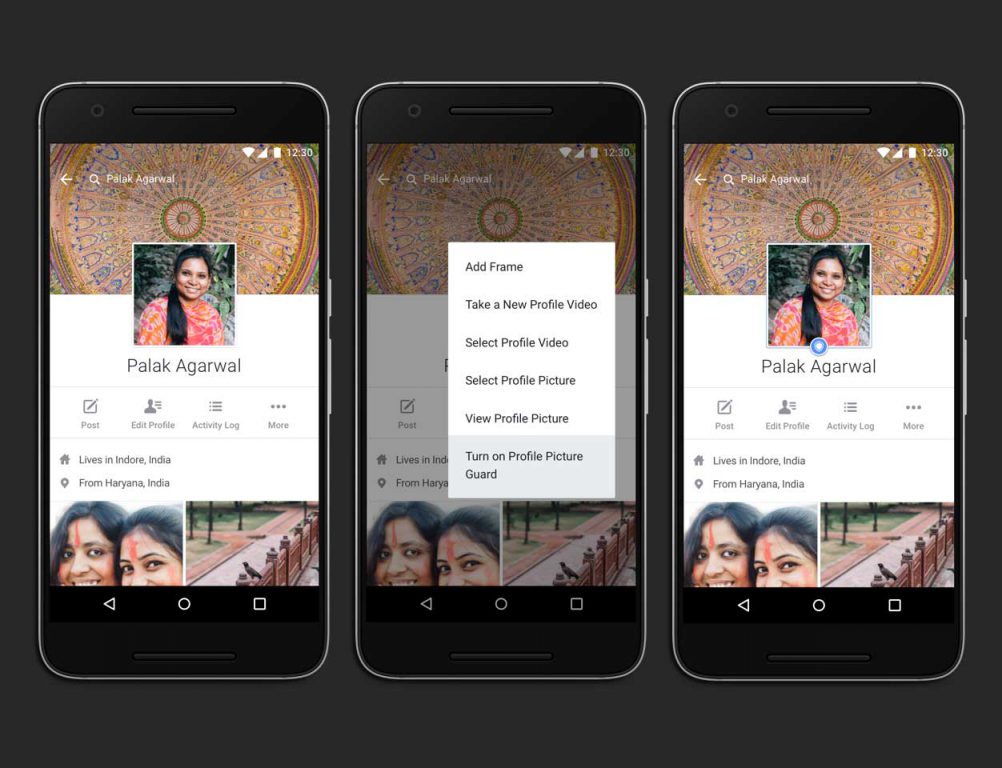
This week, Facebook India launched a new tool called the Profile Picture Guard, which is aimed at preventing misuse of profile pictures by third parties and thereby giving an enhanced sense of privacy and safety to the users. But how well can it actually protect user privacy? Continue reading “Facebook Profile Picture Guard: Completely Preventive or just a Deterrent?”
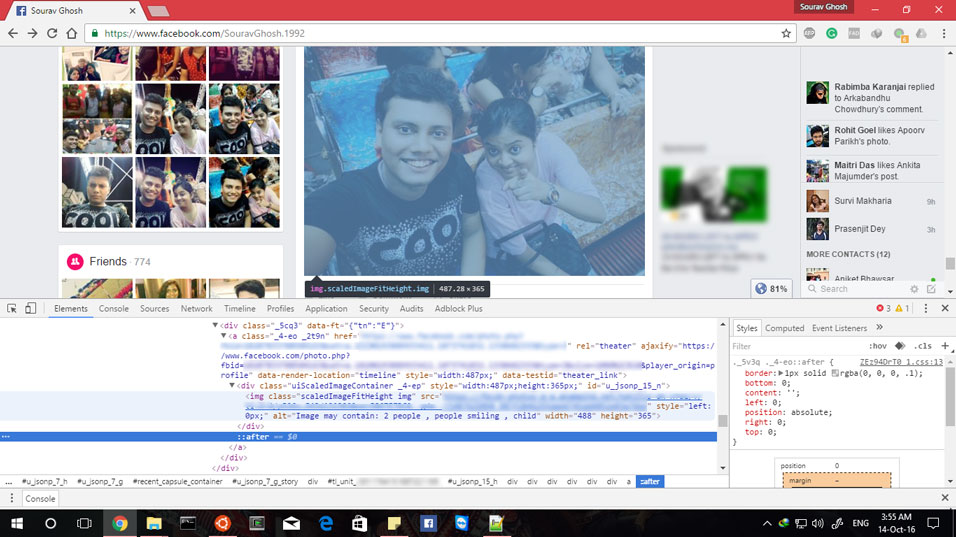
Facebook employing Image Recognition in Accessibility: An Informal Evaluation
Image recognition, especially, facial recognition is nothing new to casual users of smartphones and social networks. Many social networks including Facebook has been using facial recognition to suggest the names of “friends” while tagging newly uploaded photos. With increasing confidence values provided by modified algorithms, apps like Facebook Moments now boldly suggests that you send photos to recognised friends who feature in them. Extensive research work is being carried out in the domain of image recognition by academics and companies to further this kind of applications. In a paper titled “DeepFace: Closing the Gap to Human-Level Performance in Face Verification”, Taigman et. al. have proposed an approach for face recognition in unconstrained images which performs remarkably with an “accuracy of 97.35% on the Labeled Faces in the Wild (LFW) dataset”. That is almost at the brink of human level accuracy!
In this article, I am going to informally evaluate a new application Facebook is putting its algorithms into. A few months ago, Facebook announced that to aid the perception of photos by differently abled users who have impaired eyesight, it is going to add detected features in the alt-text of images which can then be used by text-to-speech applications to describe the image contents. Continue reading “Facebook employing Image Recognition in Accessibility: An Informal Evaluation”
The Making of a Master Key: An alternative take on the ongoing Apple vs. FBI battle over iPhone security bypass request
Being the netizens that our generation is mostly comprised of, it may perhaps be safely assumed that you might have come across some news article or tweet or a Facebook trending notification about tech-giant Apple and the FBI fighting over a certain request by the authorities to bypass the security methods of a specific iPhone. Last December in San Bernardino, a couple went on a shooting spree which took the life of 14 people and died in a shootout with police after a car chase. The authorities seized their electronics in order to learn more about them. While most of their hard drives and phones were smashed, an iPhone 5C belonging to the male attacker was discovered. This is the central device to the Apple vs. FBI fight. Continue reading “The Making of a Master Key: An alternative take on the ongoing Apple vs. FBI battle over iPhone security bypass request”
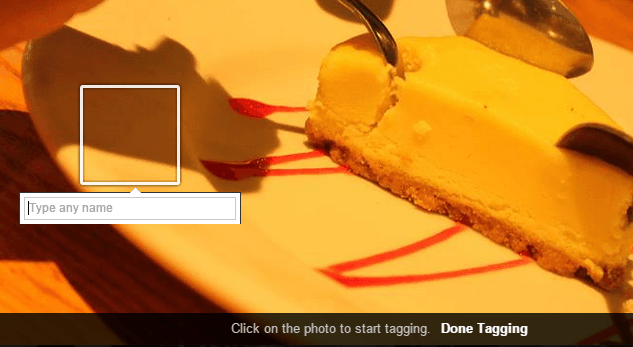
Photo tagging abuse : A chagrin of social media
Although the word “tagging” was not coined by social media, yet today it has become quite commonplace, thanks to the mass acceptance and popularity of sites like Facebook and Instagram. We take group photos, upload them on these sites, share them with out friends, but we don’t stop there. We tag the people in them!
Tagging ensures that our friends get to know that we have uploaded their photo, allows our own friends to recognise others and get to know whom we spent those awesome moments at the beach with. But it also serves another purpose – it gives us a larger audience who gets to see the photo on their news feed. And some of these strangers are sure to “like” and “comment”, aren’t they?
Continue reading “Photo tagging abuse : A chagrin of social media”
The Great Mind Challenge 2012 – An Exciting Journey
When I saw an update today on the pages that I had been monitoring for the last few weeks, and realized that it had been an entire year since we conceived the idea of our project, an indescribable feeling ran through me. It was roughly around 15th September last year when four students from our college had come together and decided to participate in IBM TGMC 2012 and test our skills against teams from all over the nation. At that time, it was merely a concept, slowly taking its shape before any actual work could begin. And today, it has been a year, and only a week since the final round results of the contest were announced, and to our extreme delight, we were declared to be amongst the winners! Let me start from the beginning… Continue reading “The Great Mind Challenge 2012 – An Exciting Journey”
Facebook rolls out Embeddable Posts to all users
Facebook announced that it was testing Embeddable posts earlier in July. This would enable users to share posts on the popular social network not only across the network but on any webpage. Initially the feature was rolled out to a few publications and pages, and after refining it considering feedback, Facebook is finally rolling out the feature to all users. Continue reading “Facebook rolls out Embeddable Posts to all users”
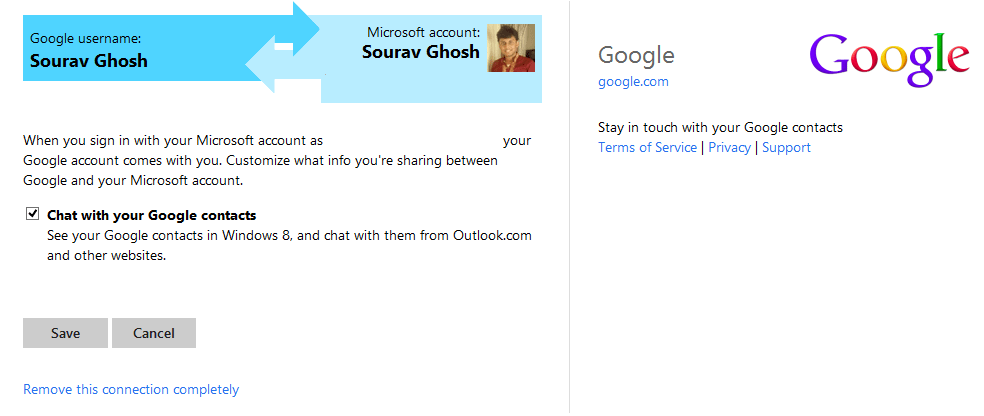
Chat with your Google contacts from Outlook.com
Email used to be once a very important part of what we called the Internet. And it is indeed one of the essence of this vast network, which still holds much importance even today when many of us are more comfortable sending short pieces of information via IM services and direct messaging clients like Facebook, BBM, and WhatsApp! Keeping this in mind, many software giants are providing chat clients embedded into their web-based email services. Google recently introduced Hangouts which replaces the older Google Talk; Microsoft recently started retiring its Messenger client, merging it with Skype; Yahoo! provides Yahoo! messenger, and so on.
Till a few days ago, Outlook.com, the renovated Hotmail service, used to allow users to chat with Messenger and Facebook contacts. Recently, the ability to chat with Google contacts was added. So, if you want to chat with your contacts on your Google account from Outlook.com,
Continue reading “Chat with your Google contacts from Outlook.com”
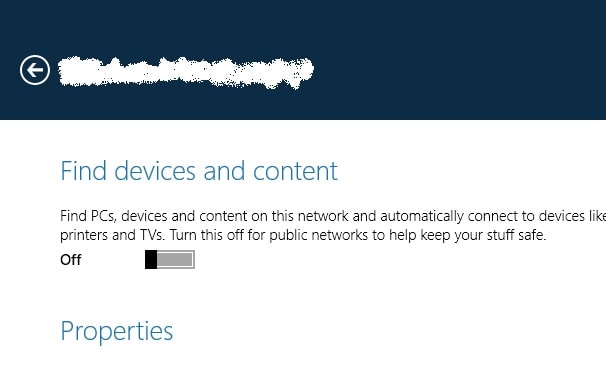
Switching Network type in Windows 8.1
Windows 8.1 Preview has just been released to the public, and in case you have installed this preview build on your machine, chances are you might have observed that some software (especially security suites) that were working perfectly in your Windows 8 machine won’t work here. It is quite normal for third-party security companies to not support beta operating systems, as the code is not final, and is subject to change. A security suite is dependent on various internal parts of the OS, and so it will take Windows 8.1 to be released to manufacturing before they are officially supported by security giants like Kaspersky and ESET. So, like it or not, for the time being, security freaks will have to do with Windows Defender and Windows Firewall.
That might be okay for quite many people who want to test a beta OS in the first place. But if you are concerned about security and have set your network type to private, then Continue reading “Switching Network type in Windows 8.1”
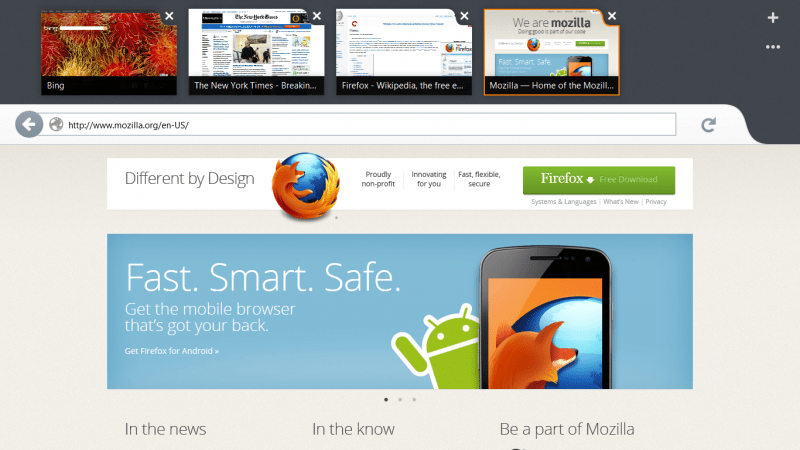
How to resume a failed download in Mozilla Firefox from the previous position
Nowadays, many of us use integrated download managers to download files of large sizes. As it is quite expected that such downloads might take quite some amount of time on typical household connections, support for pausing and resuming the download is quite important.
In modern browsers like Mozilla Firefox 22, Google Chrome 29, Internet Explorer 10, this feature is built in. However, when downloading files from servers which do not allow downloading using the same link after a certain period of time, effectively leads to the downloads getting cancelled over low-bandwidth connections if they are paused in between. Download may also fail because of many other reasons like power failure, network error, etc.
Anyway, so when it does fail using Firefox, resuming might cause the download to be restarted. Here I’ll share a simple workaround to get around this. Continue reading “How to resume a failed download in Mozilla Firefox from the previous position”